Forgot Your Password? Maybe You Can Forget It for Good! But Wait…
Tech companies are trying to develop workarounds for passwords via biometrics — facial recognition, fingerprints, and behavior patternsA tech writer — maybe not the sort of person you’d expect — confesses that he is terrible with passwords. But he is hardly alone:
In 2019, a survey conducted by Google and The Harris Poll found that 24% of Americans use “password,” “123456,” or some other ridiculously easy combination as the key to their online world. More than a third of people in the U.S. and Canada keep their passwords in notebooks or on Excel, according to a 2019 study from HYPR, the self-anointed “passwordless company.” And the same report detailed how 72% of people reuse their passwords in their professional and personal lives, while 49% just add or change a particular digit or character in their passwords when prompted by their employer. Of those last two, I will admit I am guilty.
Declan Harty, “Data Sheet: The passwordless future comes into view” at Fortune (September 20, 2021)
Here are some of 2020’s worst passwords:
123456
123456789
picture1
password
12345678
111111
123123
12345
1234567890
senha (Portuguese for password)
1234567
qwerty
Drew Todd, “Worst Passwords of 2020 List” at SecureWorld (November 2020)
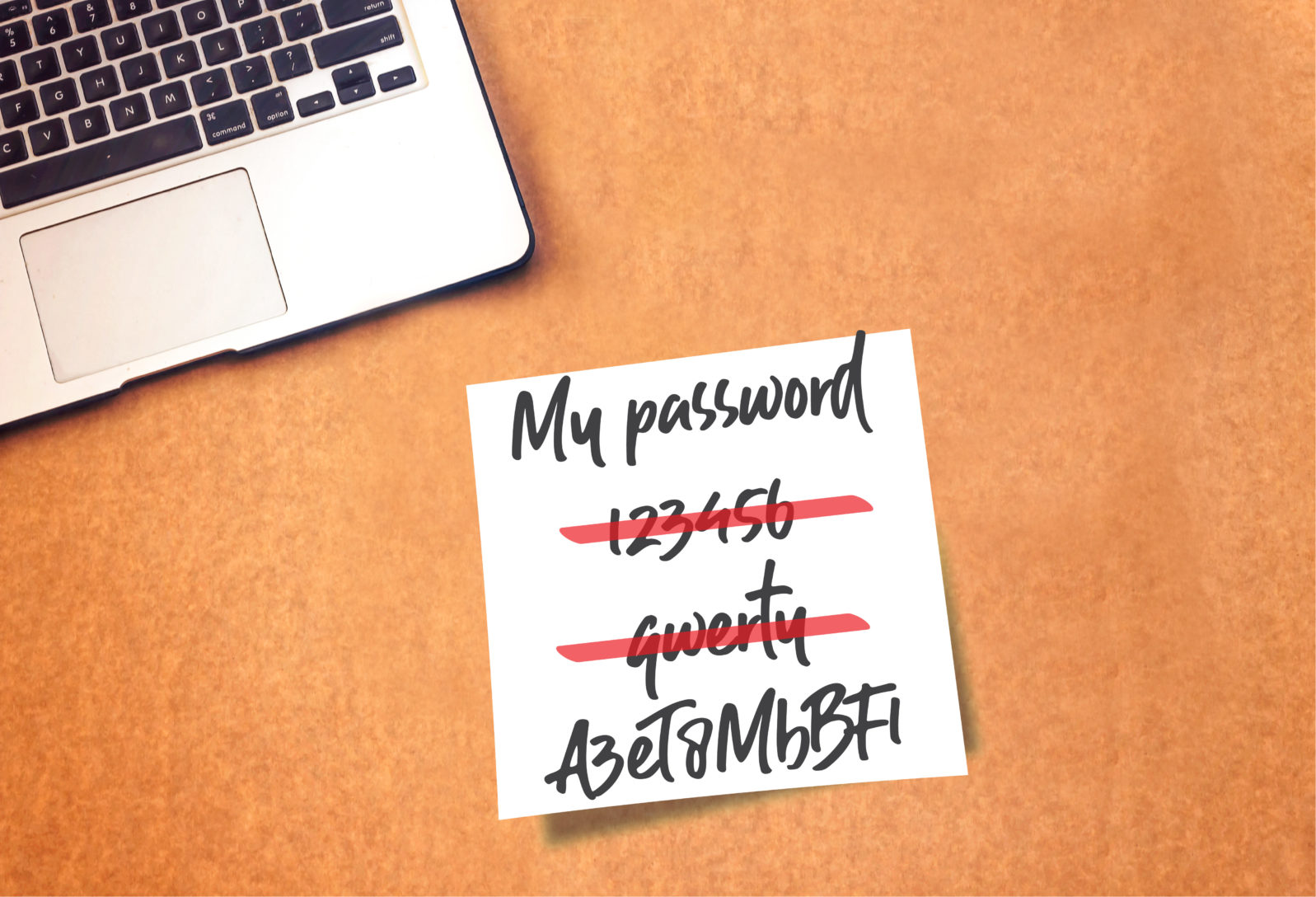
You can view some of the worst of 2019 and 2018 as well. Do any of them sound familiar?
One outcome is that Microsoft reports 18 billion password attacks per year. Computer hacks on governments, hospitals, and businesses have increased in recent years. Employees working from home during the COVID-19 crisis were often working from systems minimally (or not at all) equipped to withstand serious hacking efforts. Anyway, the information we just give away often obliterates privacy and security.
In fairness, we’re all busy. A complex password is more likely to be forgotten or misplaced. So what to do?
Microsoft has been working on eliminating passwords in favor of — to start with — multi factor authentication. Microsoft’s top security expert, Bret Arsenault has offered,
“We all sort of declared years ago that identity would be our new perimeter. People are very focused on taking advantage of identity, it’s become a classic: hackers don’t break in, they log in. I see that as a huge, huge thing for us to work on,” he said.
“Password spraying” is an old-school method, where an attacker tries to access a huge number of accounts at once using some of the most commonly used passwords. It’s simple but effective, especially where organizations don’t have additional ways to authenticate their employees.
Once an attacker is able to gain access to a network through just one employee identity with one commonly used password, he or she can begin to do more damaging work, like stealing corporate information or impersonating employees to execute a financial scam.
“The reality is, we still see a lot of attempts of people trying to password spray. The best way to protect against the password spray is to just eliminate passwords. If you have passwords, you have to enable multi-factor authentication” — that is, using a password in combination with another form m of identification, like a random set of numbers texted to the user’s phone.
Kate Fazzini, “Microsoft’s security chief explains why the company is eliminating passwords” at CNBC.com (May 1, 2019)
We’re all used to that now. And what’s the next step? Biometrics, probably. That is, facial recognition and fingerprints. Maybe iris scans. But the metrics proposed go well beyond fingerprints and include behavior:
This is biometrics not based on physical identifiers like fingerprints or scans of the iris, but rather the analysis of a user’s behavior to determine their identity.
Going far beyond technologies like voice and signatures, behavioral biometrics can focus on anything from finger movements to hand tremors and hand-eye coordination.
It can even be determined how well the user knows the information they are being asked to submit, or how familiar they are with the app they’re trying to gain access to.
“Recent research has proved that behavioral biometrics have the potential to identify a smartphone owner with high accuracy,” Abdulaziz says.
“Most of these studies use different approaches like touchscreen, keystroke, gait, behavioral profiling etc., and show each subject has a unique identity. Behavioral biometrics does not need more sensors, so the cost of building any device will not increase.
Binary District Journal, “The case against traditional passwords — and how biometrics can better secure us” at The Next Web (October 2, 2019)
Many people are uncomfortable with ideas like behavioral biometrics and it is not entirely clear that they will solve the hacking problem anyway:
Most, if not all, of the user devices that come with a biometrics login accept the biometric login as well as the default password login.
Let me try to make the relation of the biometrics and the ‘default password’ clearer with the picture of a house with a front door of a deterministic password login, to which a back door of probabilistic biometrics login was added as another entrance.
Residents are required to use the seemingly convenient back door as the first choice for entry, until they get falsely rejected there by the probabilistic biometrics. The residents rejected at the backdoor would be required to try the front door of a deterministic password login. The correct residents with correct memory are expected to be accepted deterministically.
If the one-door house was not secure enough in the first place, the two-doored house is made even less secure. Bad guys, who are now given the chance to break the back door as well as the front door, can enjoy an increased attack surface., i.e., lowered defence.
Therefore the view that biometrics contributes to identity security is false.
Christine Horton, “Why the password isn’t an enemy of people” at Think Digital Partners (August 25, 2021)
Whether or not biometrics work any better, they are likely to be promoted in and by an industry that senses a need to do something about cybercrime. What else they do is another matter.
You may also wish to read: Fallout from Facebook’s huge privacy hack: A serious unfriending. The Big Hack in April, in which even Mark Zuckerberg’s data got scraped, was hardly the first one Facebook faced.
